Most recent

AI-Enabled Social Engineering: The Attacker's Stack
AI is industrializing social engineering. Learn how attackers are building their stack—and what defenders must do before the window closes.

AiTM at Scale: What the Code of Conduct Campaign Reveals About Detection Architecture
A credential-theft campaign reached 35,000 users and cleared every automated control in the enterprise stack. Here's how adversary-in-the-middle attacks exploit the psychology of compliance — and what it takes to stop them.

Awareness Without Agency: Why Security Culture Needs Empowered People
Security awareness programs are failing — employees don't care, but organizations often don't give them the tools or agency to act.

Come see us at RSAC™ 2026 Conference
Humanix has been selected as an RSA Innovation Sandbox finalist — one of the most competitive and respected recognitions in cybersecurity, awarded to a Top 10 group.

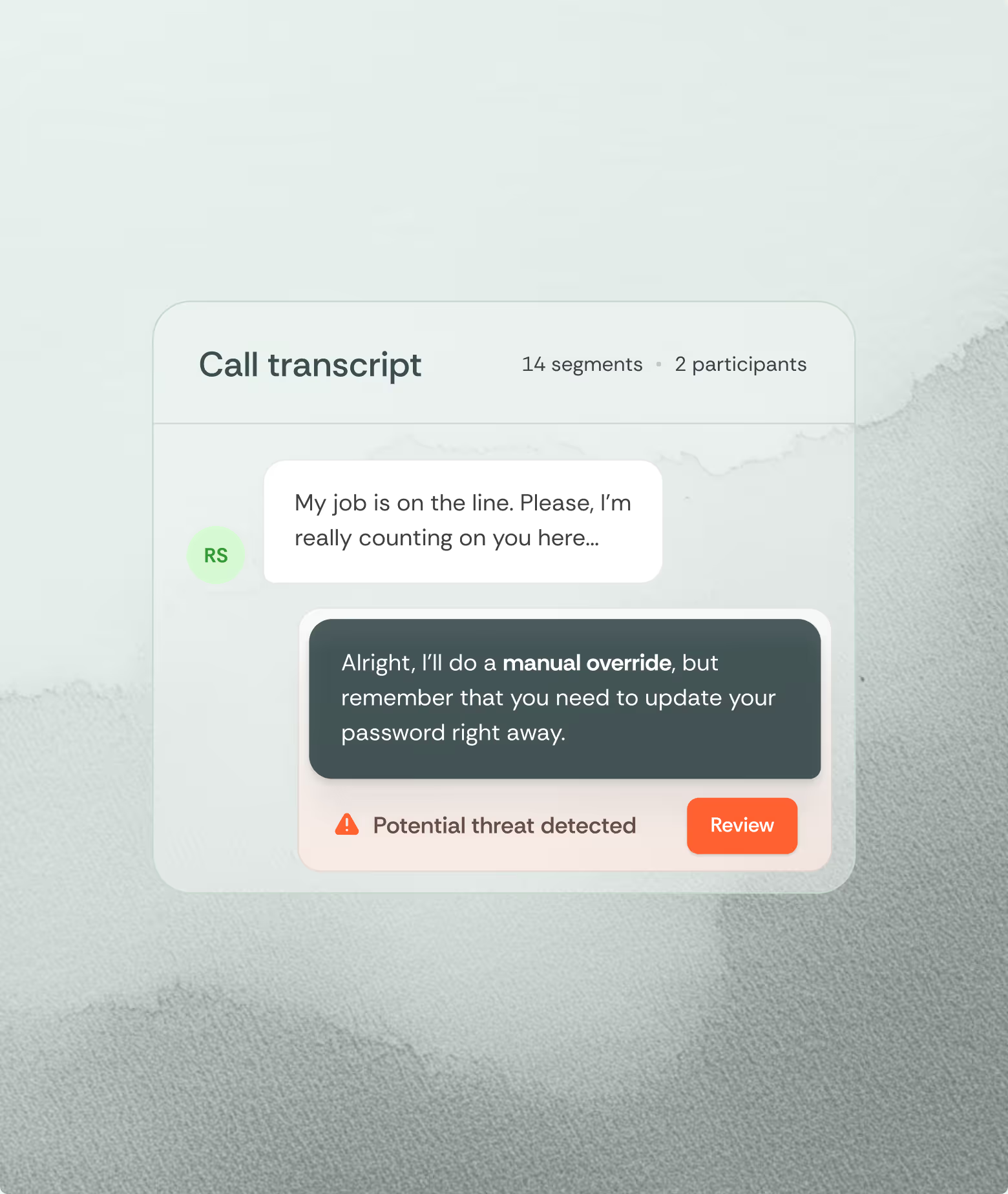
Engineered Trust: Detecting Pretexting Attacks that Play the Long Game
This piece examines the psychological mechanics behind long-con pretexting attacks and why traditional defenses fail once trust has already been operationalized.
Social Engineering: It’s a Psychology Problem
Social engineering demands psychology-based solutions, not just security policies and employee training.