With Axios, Attackers Targeted Something Deeper than Code

There's a New Attack Strategy: Engineering Compliance with Rich Social and Digital Environments.
The Axios supply chain attack will be remembered as a technical failure. It wasn't. It was an understandable cognitive failure in a simulated social environment. The malicious code was just the last step. This piece examines the mechanisms that made it work — and why current frameworks for understanding these attacks miss why they succeed.
The recent attack on Axios that compromised a JavaScript library downloaded over 70 million times a week didn’t start with malicious code, a spoofed email, or a suspicious attachment. It started with social engineering that began days before the suspicious request was made. By the time it came, it was no longer suspicious but couched in a bubble created for deception.
Employees who are social engineered are often derided (or fired) for their purported gullibility. Decision science would label these accusations as hindsight bias: imposing our current knowledge onto people and past events where and when it might not have been available.
The attack illustrates the power of the pretext: a meticulously researched and constructed illusion of legitimacy developed before the victim receives the request. As people begin to spend increasingly more time online in their work and social lives, what matters most is that this environment seems real. Developments in large language models, deepfakes, etc., make the cost of building a social engineering task nearly zero.
Pre-Texting and Pre-Suasion
By the time the threat group made contact with Jason Saayman, the [lead] maintainer of one of the most widely used JavaScript libraries in the world, the trap had already been built for him. It only required that he walk into it. And that was part of his job. This was not an ad hoc attempt, it was a concerted attack by a state-backed group. The technical execution was sophisticated. The psychological mechanisms were not.
The attack group, UNC1069, didn’t present Jason with a fabricated identity or suspicious link or attachment. They presented him with a reality: an environment filled with staff, conversations, projects - all the features of a real workplace.
There’s nothing new here. Cialdini calls this pre-suasion: environments are built to nudge us forward, selectively present information, and prime us to interpret new experience in ways that serve the engineer’s purpose. This is the same process that makes disinformation campaigns successful: when someone reaches into their environment or looks into their memories, they find the information that social engineers want them to find.
Consider Jason’s account on GitHub:
”[T]hey had cloned the [company’s] founders likeness as well as the company itself. [T]hey then invited me to a real [Slack] workspace. [T]his workspace was branded to the companies [CI] and named in a plausible manner. [T]he slack was thought out very well, they had channels where they were sharing [Linked-In] posts, [the posts I] presume just went to the real [company’s] account but it was super convincing … [T]hey even had what [I] presume were fake profiles of the team of the company but also number of other [OSS] maintainers…
[T]he [message in the] meeting [on MS Teams] said something on my system was out of date. [I] installed the missing item as [I] presumed it was something to do with [Teams], and this was the RAT.’”
We don’t understand the world directly, we use cues we’ve learned from prior experience. The environment is convincing because of all the cues that are there. In low-fidelity environments like those in digital environments such as online workspaces or websites, the number of cues needed will be smaller than those in the physical world. The more we become used to these authenticity cues, the easier it is for us to be convinced.
But it’s not just the digital environment. His account speaks to the social environment:
”[T]hey scheduled a meeting with me to connect. [T]he meeting was on [MS Teams] [and] had what seemed to be a group of people that were involved.”
This pretext combines sets of cues across physical and social channels. These were all cues to legitimacy. It’s coherent. It’s immersive. It’s impressive. And it’s easier to create than it has ever been.
We’d be mistaken to discount Jason’s experience. Every signal available to him was pointing in the same direction by design. Even if security training provided employees with the basic features of social engineering — making sense of a set of cues across channels in real-time is a daunting task: he was on a Teams call and software needed to be updated. This is a common experience. And social engineers know that.
The New Playbook: Personalization and Industrialization
This era of attacks moves us away from hastily typed emails in poor English and sloppy graphics. AI has shifted us into a new era where, given a few prompts and a few minutes, realistic cues can be cloned and created. But the key is personalization. Personalization is what makes the attack believable. Scale is what makes it inevitable.
Generic phishing scams feel impersonal. They invoke general time pressure, institutions, or common crises that are plausible but don’t align with our experience. By forcing us to think, the cognitive friction takes enough time for us to slow down. As the cues activate our memories, we begin to see the loose connections. Increase the pace, and there isn’t enough time to reflect.
But Jason’s experience is not isolated. He’s just brave enough to speak up. The same campaign targeted multiple maintainers across the Node.js ecosystem.
What was once reserved for high-value targets can now be used against people who maintain the infrastructure that everyone relies on. While the playbook remains the same, the economics have changed. AI-generated worlds can be created in minutes, honed in hours. The resources that would be selectively targeted at an executive, a founder, or financial decision makers can now be spread across hundreds within an organization. In this numbers game, attackers win.
The Need for a Cognitive Approach
The Axios attack will be categorized as a supply chain attack. This is a familiar category, codified in MITRE ATT&CK and other prominent frameworks. But the comfort of naming these events created cognitive debt: it misses the critical nuances that make them work.
The technical effects are downstream from the real source of the issues: social-cognitive processes that adversaries exploit. Frameworks have focused on attack cycles, attacker’s processes, and motivational factors such as commitment, trust, obedience to authority. More ambitious frameworks have attempted to integrate cognitive processes with attacker’s strategies. Each of these approaches misses the interplay between the person, the situation, and the artificial environment.
To understand these attacks we need to understand the features that define the request and how it is interpreted. What makes it work is a combination of cognitive, social, and technical factors that work together.
1. The cognitive processes that are targeted. Basic processes such as attention, memory, and decision-making must be coordinated to make sense of the environment. Individual features or entire schemas can be activated. If the pattern individually or collectively looks familiar, people are likely to use less mental effort - directing it to more complicated tasks.
In the Axios case, the key to the deception is pattern recognition. The Slack workspace, the fake team profiles, and the LinkedIn reposts provided evidence that accumulates over time. In isolation or paired with incongruent patterns, they wouldn’t work. Together, it represents a coordinated attack on Jason’s thinking.
2. The relationships being targeted and what are their defining properties. Trust is based on relationships. Relationships are defined by asymmetries in what information is sought and how it is requested. These create the social scripts that people live by. Choose the right script and populate it with the right case of characters and compliance follows automatically.
The unique feature - and likely success of the Axios attack - is that it created a reality. This was not a 2D institution that only had a name and a fabricated website, Jason stepped into a complete, active social world that was created from nothing.
Critically, the attackers didn’t rush this rapport building. They developed it slowly over time. This increases the realism. UNC1069 developed and exploited the relational trust. If organizations cannot trust partnerships they build with others, business cannot proceed.
3. The cognitive load and cognitive resources available. Every task has its own cognitive load. Experience can reduce this load while multi-tasking can decrease what mental resources are available. In most workplaces, employees are expected to balance multiple tasks simultaneously.
Jason was on a Teams call, actively managing a social interaction with new people, processing audio and video, and simultaneously presented with a software prompt. This is a reasonably high load. The social script that is already active and the exchange was ongoing. The software update would inhibit that flow. The attack was timed and structured to maximum effect.
It’s also safe to say that there is a chronic load hidden from Jason’s account. There are other events in the workplace and in our personal lives that keep us preoccupied.
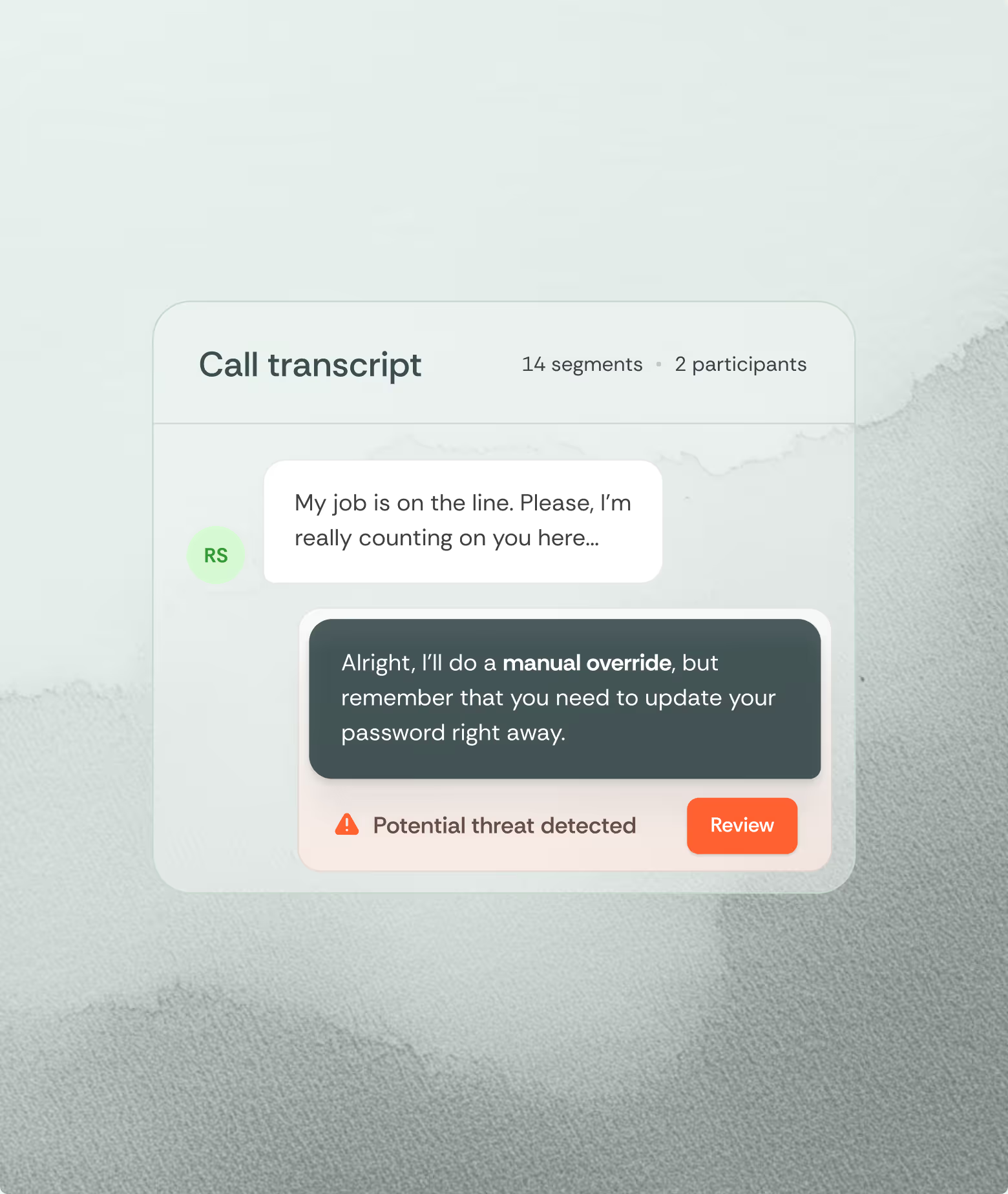
4. Affordances of compliance. Digital environments are designed to direct our attention and promote certain actions. Buttons are positioned in familiar places and notifications are designed to prompt us to take helpful action. Attackers know this.
In the Axios case, the software update prompt was the endpoint of a carefully constructed social and technical sequence. It was the only thing slowing down their interaction - something that we see every day. In that environment, compliance was the natural move.
General security training cannot equip people to address this. Most training focuses on a suspicious request, with a small set of discrepant cues or time pressure. The Axios attack was a multi-day, multi-step, pretext, every detail deliberate. The environment was designed to persuade him. From the perspective of cognition, the time scale of the attack was too long, the cues too weak, and the information environment too complex. Without a cognitive scaffold to help track these pieces, it is unrealistic to expect that such attacks can be stopped.
Calling it a supply chain attack is not wrong, it's simply incomplete. It was an attack on the very mental and social processes that allow the supply chain to exist.
What is feature engineering
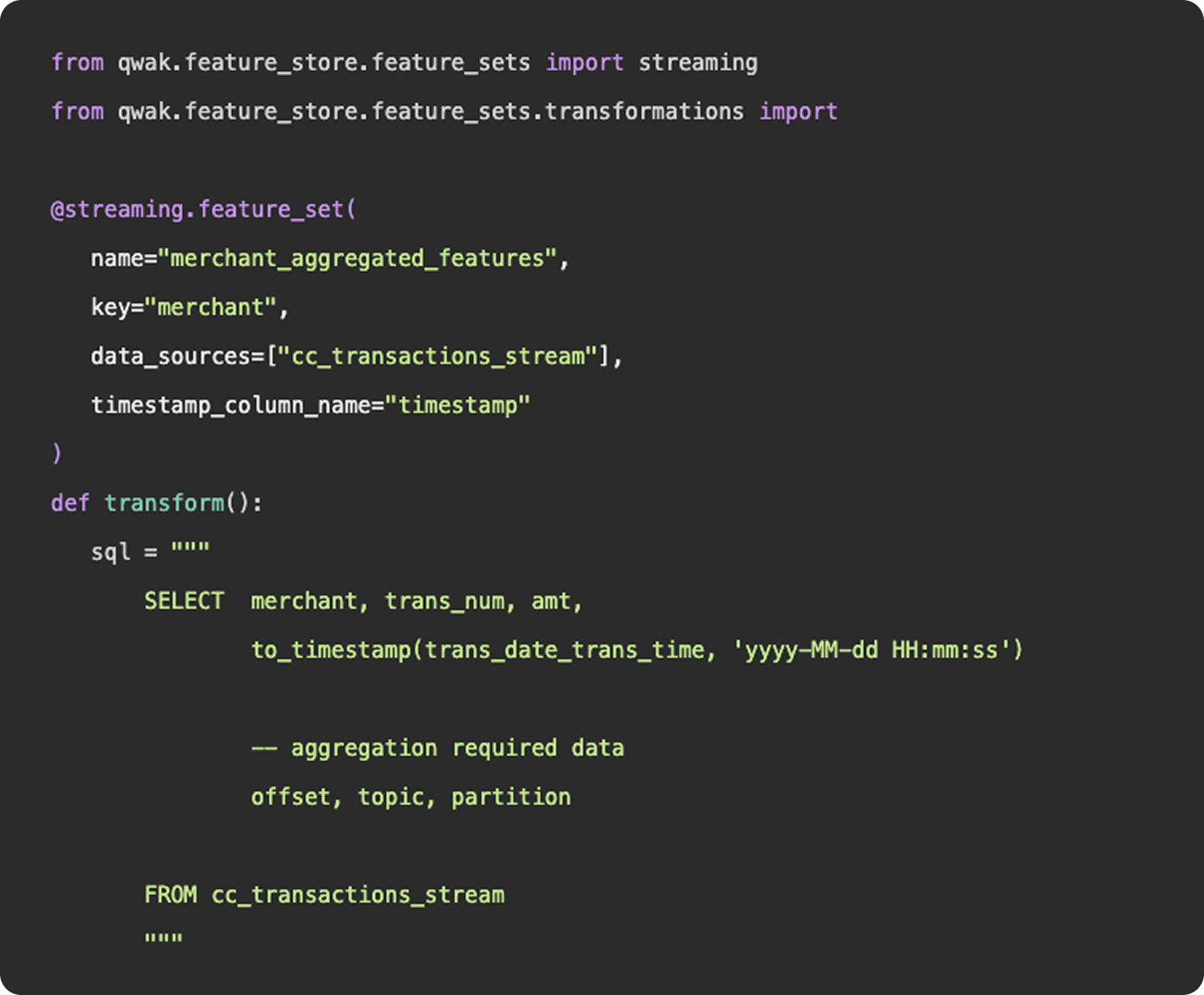
In practice, feature engineering is both science and a bit of witchcraft. It often involves both iteration and experimentation to uncover hidden patterns and relationships within the data. For instance, a data scientist might transform raw sales data into features such as average purchase value, purchase frequency, or customer lifetime value, which can significantly boost the performance of a churn prediction model. By thoughtfully engineering features, practitioners can provide machine learning models with the most informative inputs, ultimately leading to better accuracy and more robust predictions.
What’s more?
- Incorporate more and more data sources
- Feature engineering platform
What is data engineering
As we mentioned above, feature engineering is certainly a subset of data engineering. It involves the ingestion of data from a source, applying a series of transformations, and making the final result available to be queried by a model for training purposes. You can construct feature engineering pipelines to resemble data engineering pipelines, having schedules, specific source and sink destinations, and availability for querying. However, this configuration would only really apply once you have surpassed the experimentation stage and determined a need for a consistent flow of new feature data.
What is feature engineering
1. Functions
Functionally, there is nothing to differentiate data vs features - data points (link). Where feature engineering and data engineering really differ is in the objectives and motivations for constructing the pipelines. In general, data engineering serves a broader, more unified purpose than feature engineering. Data engineering platforms are constructed to be flexible and universal, ingesting various types and sources of data into a unified storage location where any number of transformations and use cases can be applied. The intent of a well constructed fact table or gold layer in a data lake is to provide a single source of truth that answers many different questions, produces many reports, and can be consumed by many downstream customers.
2. Practise
And in practice, an organization’s data engineering team will be responsible for the curation and maintenance of all data pipelines, not just those that relate to machine learning. These pipelines may power BI dashboards used by C-Suite, auditing reports that feed payroll, or event logs that show a user’s history of actions within the application.
Feature engineering, on the other hand, serves a specific purpose, finding the tailored inputs and columns that will generate the best predictive results for a machine learning model. Data scientists and machine learning engineers are not tasked with developing a universal data model that will ingest all data points throughout an organization, they just need to select, curate, and clean the data needed to power their models.
3. Machine learning
Now, as machine learning teams grow and begin to incorporate more and more data sources into their models, their feature engineering platform may start to resemble a larger data engineering platform in the tools and methodologies they employ. But, the intent is not to establish flexible data models that can be used throughout the organization - it is simply to power their machine learning models.